Personal Historical Benchmark Tests and Screens…& CPUz/GPUz/TC Comparisons…& More…
Category Archives: Antikeymagic
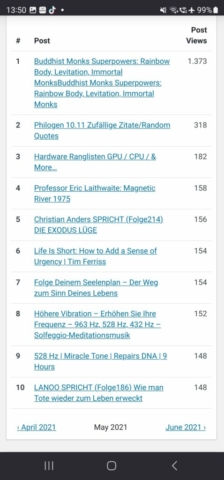
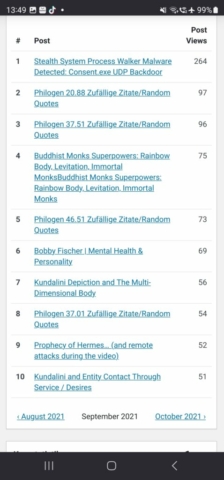
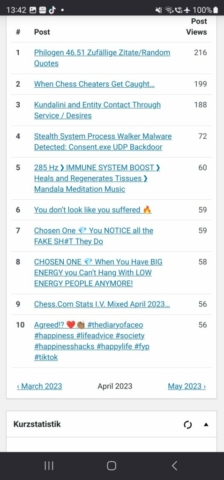
Viewer Statistics show me that you lust for Antikeymagic Level 10+…. (2021/1 – 2023/10)
IT Security Archive 3 – Retro News – FB & CPU Trojan – Extended Saga Continues – Zombiehost Trojan Facebook
IT Security Archive 3 – Retro News – Zombiehost Trojan Facebook – 24. November 2015 ·
Comodo v8.0.4x finally reacts on consent.exe-Akamai-FB-Exploit…Post-Logon-Firewall-Bypass-Essay by NSA & Co. Process-Shadow-Walker. It says consent.exe is secure, but not its payload… 😉

„NetRange: 108.162.192.0 – 108.162.255.255
CIDR: 108.162.192.0/18
NetName: CLOUDFLARENET
NetHandle: NET-108-162-192-0-1
Parent: NET108 (NET-108-0-0-0-0)
NetType: Direct Assignment
OriginAS: AS13335
Organization: Cloudflare, Inc. (CLOUD14)
RegDate: 2011-10-28
Updated: 2017-02-17
Comment: All Cloudflare abuse reporting can be done via https://www.cloudflare.com/abuse
OrgName: Cloudflare, Inc.
OrgId: CLOUD14
Address: 101 Townsend Street
City: San Francisco
StateProv: CA
PostalCode: 94107
Country: US
RegDate: 2010-07-09
Updated: 2017-02-17“
ITSecurityArchive3· 24. November 2015 ·
Remember I didn´t open any Browser…that´s what the NSA does with Targeted Systems when you connect on Facebook and you are considered „important“ enough to be taken into consideration…Corporatistic fraudulent Cyber-terrorism…
(6.11.2015) /(IT-Security) /Facebook /(Sabotage) /DOD /(Spy) /(Agencies) /(Software) /(Fehler) /(Forensik) /(ShadowGov) /(Public Counterintelligence) [23339]

ITSecurityArchive3 · 8. November 2015 ·
Wenn ich IP-Blocked „Amazon Technologies Inc.“ lese fällt mir realistischerweise nur NSA ein… „wink“-Emoticon 1
ITSecurityArchive3 · 11. Juli 2017:
I don´t take that personally…the FB-Criminal-Corporate-Alphabet-Gang-Trojan-Zombiehost-CMOS-Exploit uses a heuristic attack and delay mechanism for all potential security and defense tools that could remove it…
The Anti-SEC Gov-Mafiosis – former criminal hackers – are in Dreamland…they get highly paid from the Gangster Government for doing script kiddie style mass sabotage…
ITSecurityArchive3· 24. Juni 2017 ·
Why it is a bad idea to give the Department of War and Zion backdoor access to each commercial CPU on the Planet…
CPU Thermal Deception…this forces the CPU to throttle down… Delay Tactics… In Reality the Temperature of the CPU is around 50-60 °C…but thanks to morons who play with the DOD CPU Backdoor on FaceBUG you get this…

5. Februar 2017 · Reminder… this procedure didn´t change and is ubiquitous…connection with FaceBUG means Shadow Gov Implantation…all the more strange that people don´t want an effective antidote….
ITSecurityArchive3 · 8. August 2016 ·
1.7.2016.
OUROBOUROUS SYSIPHUS INFINITY….FEDERAL CRIME SYNDICATE FraudBUG…
/
They reacted immediately with a Cyber-Attack…;)
1 OBJECTIVE PROOF AND IRREFUTABLE EXPOSE is enough…

ITSecurityArchive3· 8. August 2016 ·
See this then get used to NSA Attacks or Trash your system…
NO CORPORATE ANTIVIRUS OR SECURITY SUITE OR FIREWALL WILL HELP YOU…they all help the GOVERNMENT (whether they are aware or not – they are bypassed either way by the Corporate Gov Contractor Criminals)…except you know some UNDERGROUND TOOLs… 😉

ITSecurityArchive3 · 6. August 2016 ·
10. Juli 2014 · Little Message to the troublemakers… I noticed your Exploit.

ITSecurityArchive3 · 10. Dezember 2015 ·
That´s why TOR won´t save your privacy… get it? 😉
Backdoors to the Bone from Humans to Computers…;)

„NetRange: 198.41.128.0 – 198.41.255.255
CIDR: 198.41.128.0/17
NetName: CLOUDFLARENET
NetHandle: NET-198-41-128-0-1
Parent: NET198 (NET-198-0-0-0-0)
NetType: Direct Assignment
OriginAS: AS13335
Organization: Cloudflare, Inc. (CLOUD14)
RegDate: 2012-10-09
Updated: 2017-02-17
Comment: All Cloudflare abuse reporting can be done via https://www.cloudflare.com/abuse
OrgName: Cloudflare, Inc.
OrgId: CLOUD14
Address: 101 Townsend Street
City: San Francisco
StateProv: CA
PostalCode: 94107
Country: US
RegDate: 2010-07-09
Updated: 2017-02-17“
Schließen
ITSecurityArchive3 · 6. August 2016 ·
5.140.xxx.xxx Akamai + Limelight …u.a. hängen sie sich auch in Level 5 Nodes rein…MITM…
/
95.100.186.128
abuse@akamai.com
inetnum: 95.100.176.0 – 95.100.191.255
netname: AKAMAI-PA
descr: Akamai Technologies
country: EU
created: 2010-07-30T13:01:49Z
last-modified: 2010-07-30T13:01:49Z
source: RIPE
role: Network Architecture Role Account
address: Akamai Technologies
address: 8 Cambridge Center
address: Cambridge, MA 02142
![]()
Software Failures – 6. August 2016:
History of the GANGSTERBOOK.. Implantation and their Sabotage actions will be found here….
Das Non-Existent Syndrom von FACE-The-Man-In-The-Middle-WANZEN-BUCH…Ich habe die Lösung gegen die U.S. Shadow-Schurkenmacht…

5. Februar 2017 · Antikeymagic even protects poor victim firewalls of the crime syndicate attacks on Hellbook…
//
ITSecurityArchive3
24. Juni 2017
I want to see a rise of non-governmental non-compromised hardware and software manufacturers that are so hardened that the silly alphabet gangs and criminal governments with their stolen script kiddie tools from Russia will have no chance to break through…. The touchstone and criterion will be the Zion Global Crime Cartel CIA DIA DOD NSA MI GCHQ BND NIH NASA DARPA Censor Central called Facebook. Usually their Aggressive AI needs only 2 to 3 weeks to break every corporate security company and every firewall autonomously..and usually with the first login and the first reboot you get their Zombiehost.Infector.Implant and later on the CMOS.Infector (I remember vaguely that they called it Deity Bounce and before the rise of UEFI BadBIos).
ITSecurityArchive3
24. Juni 2017
Except that Antikeymagic removes all your NSA sabotage effects..we don´t see the demons…but we can reverse their adverse imposition…see below ATKM Logs and Vids give you proof enough…
But Zombiehost is visible and can be combatted…your rootkit injector might be invisible.
/“Closing Thoughts: Hypotheses on DEITYBOUNCE Technical Purpose
There are two undeniable strategic values possessed by DEITYBOUNCE compared to “ordinary” malware:
DEITYBOUNCE provides a stealthy way to alter the loaded OS without leaving a trace on the storage device, i.e., HDD or SSD, in order to avoid being detected via “ordinary” computer forensic procedures. Why? Because the OS is manipulated when it’s loaded to RAM, the OS installation on the storage device itself is left untouched (genuine). SMM code execution provides a way to conceal the code execution from possible OS integrity checks by other-party scanners. In this respect, we can view DEITYBOUNCE as a very sophisticated malware dropper.
DEITYBOUNCE provides a way to preserve the presence of the malware in the target system because it is persistent against OS reinstallation.“
https://resources.infosecinstitute.com/nsa-bios-backdoor-god-mode-malware-deitybounce/#gref
ITSecurityArchive3
24. Juni 2017
Niemals mit wertvollen Systemen bei Google oder Betrugsbuch FakeBUG einloggen…sonst könnt ihr gleich ein neues BIOS/CMOS kaufen… und das wird dann reinfiziert…also ist es besser erstmal mit einem verseuchten alten System zu surfen und Antikeymagic zu benutzen…
ITSecurityArchive3
24. Juni 2017 ·
Remember the former Guys from Rootkit.com are now your Government and Spy Gangster Agency invaders… So the old rule that hackers are against Governments is out…they are all sitting as a cronyist cliquishness together against all unwitting civilians….who have 0 knowledge and 0 defense possibilities against this criminal cartel.
ITSecurityArchive3
5. Juni 2017 ·
Die Zombiehost Wanze funkt über eine IP von Telefonica München raus…Stasi 5.0. CMOS.Persistenz.Infector.2017.1.15.Ami.RAM.Limiter.Coldwarmboot.Disruptor.BND.CIA.NSA.DOD.DARPA.Crime Syndicate Inc. Implant wird über Facebug login.browser.stealth.0.0.0.0.tunnel.exploit abgeliefert…in alle anfälligen Systeme.
Am liebsten haben sie natürlich Windows.
ITSecurityArchive3
24. Juni 2017 ·
9.6.2017
CPU-Delay-Tactics of Intels-DOD-Cpu-Trojan…. When they see Antikeymagic they get an allergic shock..similar to chrome based browsers..they try to delay everything…and might brake the speed of your CPU….lol…it´s insane what is going on…beyond any rational intelligence.
ITSecurityArchive3
24. Juni 2017 ·
In Germany too…it is such a freaking Joke..the whole IT Security business is the biggest farce in the Universe…and I say it again currently only Antikeymagic can freeze the FaceBUG.CIA.Zombiehost. CMOS.Infector for Windows Systems and re-enable all disabled security tools..from the Software side… It is not only WIFI, also Wired Routers have all a backdoor and each CPU has a DOD Trojan.
/
„CIA has access to your home router, as well as every WiFi system in the United States, warns internet security chief John McAfee.
John McAfee: Every router in America has been compromised‘
John McAfee talks on RT about the insecurity of the modern network and the vulnerabilities we all share.“
ITSecurityArchive3
3. Juli 2017 ·
Wir sollten es der Regierungsmafia schwieriger machen…..wenn man auf Virusdelaycensor-Honeypot einloggt…..und die verkommene Oberverbrechermafiaregierung des bestialischen Zion-Imperiums will Linux nun auch restriktieren.. Ihr scheiss Bundestrojaner ist so ausgereift wie ein billiger script kiddie Trojaner, der das System in den Zeitlupenmodus versetzt und viele Windows-Systeme einfach nur browsernavigierunfähig macht…
Vergessen zu erwähnen..das browserdelay Zombie- Implant der FB GeStaPo verlangsamt auch viele Android Smartphones. DoD CPU throttle harassment…also linuxartige Versionen werden auch schon angegangen..
3. Juli 2017 ·
Message for All who use Windows (they surely do similar things with other OS) with CIA-Book,,,they also infect your USB Sticks and your OFFLine Computers….just a little info…This Criminal Cartel Central called Facebook is Zion CIA DOD NSA DARPA DIA GCHQ BND Alphabet Plagues main online viral infector vector…It´s a dream for the Gangster Empire…
ITSecurityArchive3
1. August 2017 ·
CMOS Chip ausgewechselt…hat sich quasi alles bewahrheitet…was ich diagnostiziert hatte…ich logge hier nicht mehr mit guter Hardware ein… Der Facebook. CMOS.DOD.CIA.BND.Zombiehost.Extension.Sabotage.Virus hatte 50% vom Ram abgeschnitten und die interne Intel CPU Graka deaktiviert…und weitere noch nicht bekannte Teile des Coldbootvorgangs sabotiert… nach CMOS Wechsel ist der RAM wieder voll aktiv und die interne CPU Graka funktioniert wieder…
ITSecurityArchive3
14. August 2017 ·
I removed the one I caught from CIA-FaceBUG… since 15.1.2017 CIA/DOD/NSA/ARPA-Facebook also implants systems with CMOS-Infector + Zombiehost.
“The idea is to make it obvious that these secure boot disk style things are architecturally vulnerable to attackers who come at you from the BIOS level space.”
The implant works on BIOS variants of many vendors and according to the expert, the BIOS bootkit is effective also against UEFI, that is considered the evolution of the BIOS.“
http://securityaffairs.co/wordpress/35097/hacking/researchers-developed-bios-bootkit.html
ITSecurityArchive3 hat einen Beitrag geteilt.
16. August 2017 ·
Itsecurityarchive2
15. August 2015 ·
„Möglich macht das ein Design-Fehler in CPUs aus den Jahren 1997 bis 2010. Angreifer können ihn verwenden, um Schadsoftware in einem Bereich zu installieren, der für die Sicherheit auf Firmware-Ebene verantwortlich ist. Sicherheitsfunktionen wie Secure Boot funktionieren anschließend nicht mehr.
Einen Angriff auf dieser Ebene ist von Antivirenprogrammen nicht zu erkennen. Auch wenn Nutzer ihre Festplatte formatieren oder das Betriebssystem neuinstallieren, bleibt eine derartige Schadsoftware erhalten. Domas habe auf der Konferenz Black Hat Beispielcode für einen Angriff vorgeführt, berichtet Computerworld.
Dem Bericht zufolge ist ein im SMM installiertes Rootkit in der Lage, das UEFI-BIOS zu löschen. Sicherheitsfunktionen wie Secure Boot sind wirkungslos.“
https://www.silicon.de/41615692/aeltere-intel-cpus-rootkits-koennen-uefi-bios-loeschen
IT-Security-Archive – Retro News 2013 bis 2017 – CPU Trojan & Antikeymagic HE vs Zombiehost 2017 – Archive Externalization
IT-Security-Archive – Retro News 2013 bis 2017 – Antikeymagic HE vs Zombiehost 2017 – Archive Externalization
IT-Security-Archive – 2. August 2017 ·
25.4.2017
You know what it means that all systems have a DOD (DOW) CPU-Trojan?
There is no property ownership possible for people who are connected to the Internet…except they encrypt all their stuff in a way that is too difficult or too annoying to decipher for „them“…
The Main Problem is DARPA/DOD/In-Q-tel,..they have a Trojan in every commercial CPU…that renders a lof of Security Software useless, except Antikeymagic at Level 10,11,12,13 that re-empowers tunneled/trojan disabled Security Software by DARPA/Department of War…They can deactivate parts of your RAM/GRACA as a means of remote digital punishment..infecting most UEFI Bioses as well.
They probably would call it their „Life-Insurance“ or their „Military Dominion over the Civilian Slaves“ Insurance (apart from their crowd control weaponry –
DARPAs Insane Motto: Weaponize and Robotize everything)…Digital as well as Biological..I read the most important summary of DARPA/Department of War/In-Q-Tel today… Backdoor everything and every living entity…and then the slaves can unleash their hate, rant and/or grief about the situation (if you are not one of those I-swallow-everything- consumer-zombies (just in case)) without problems (for them)…because they could control you (eventually) on the lowest level…in real life and in virtual life…
2. August 2017 ·
Betrifft sämtliche Windows Systeme::: #TimeMachine
21.4.2017
Bis 15.1.2017 war das kriminelle FaceBUG Zion Cartel zumindest noch so frei den Menschen zu erlauben ihre Boards selbst zu reparieren…seit besagtem Datum haben sie die Persistenz-Funktion ihrer Schadensimplantierungen aktiviert….d.h. Benutzer werden daran gehindert ihr eigenes Bios zu reparieren…vor dem 15.1.2017 konnte man das BIOS reflashen…und Antikeymagic hat gesagt: alles sauber…
Nach dem 15.1.2017 flashen die Leute ihr UEFI Bios…und Antikeymagic wird das anzeigen und die Situation für den Benutzer retten…sofern die Leute schlau genug (90% kümmern sich eh nicht drum…zu dumm, zu desinteressiert, zu gleichgültig, zu zombifiziert oder zu ignorant, zu gläubig an ihre kommerziell-korporativen Taugenichtsprogramme…) sind Sicherheitstool der besseren und überlegenen Art zu installieren…
Kein automatischer Alternativtext verfügbar.
IT-Security-Archive
18. Juni 2017 ·
WHEN LOGGING INTO FACEBOOK EVERY WINDOWS SYSTEM BECOMES INFECTED WITH ZOMBIEHOST..OBJECTIVE PROOF!
/
I could test you a 100 systems with the same results…
/
People seem to be comfortable with this unacceptable sabotage action…
//
Starte Scan nach Adware, Spyware, Risks, Worms, Keyloggern, Trojanern, Malware und Viren!
(V11.33)
__________________________________________________________________________________________
Windows7-Independent.Rootkit.Asus2009.ADSM_PData_0150(CIA)(statisch/harmlos) Verzeichnis
entdeckt! (Paranoide Heuristik 5)
Malware.Exploit.Gefahr! WerFault! Prozess entdeckt! (Prozess Heuristik 2)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess
entdeckt! (Prozess Heuristik 5)
__________________________________________________________________________________________
System Information1: Prozessor/CPU: Intel(R) Core(TM)2 Duo CPU T6600 @ 2.20GHz
System Information2: Prozessor/CPU Speed: 2195 Mhz
System Information3: Windows Version: Windows 7 Home Premium / 1 / 64 Bit
System Information4: NT Version: 6.1 BuildNr.: 7600 Organization: Microsoft
System Information5: Bekannte Sandboxen: COMODO V.8.x(7.x/6.x) /
System Information6: Bekannte virtuelle Machine: NEIN (reales System)
System Information7: Uhrzeit: 5:29:24 PM und Datum: 6/11/2017
__________________________________________________________________________________________
Peerblock reaktiviert! (5:29:26 PM – 6/11/2017) (Peerblock-Surveillor)
Malware.Exploit.Gefahr! WerFault! (WindowsCrashBugs)(5:29:26 PM – 6/11/2017) Prozess
entdeckt![Hgwt5]
Malware.Exploit.Gefahr! WerFault! (WindowsCrashBugs)(5:29:26 PM – 6/11/2017) Prozess
gestoppt![Hgwt5]
[Root:Win32k.sys] Design-Terror-Ghost-Win7 (Ghost Window) (terminable) – Win10/8
(Persistence-Winlogout-Bug) Windows Klasse entdeckt! Ring-Wächter [Hgwt3](5:29:30 PM –
6/11/2017) (Restriction Releaser)
[Root:Win32k.sys] Design-Terror-Ghost-Win7 (Ghost Window) (terminable) – Win10/8
(Persistence-Winlogout-Bug) Windows Klasse entdeckt! Ring-Wächter [Hgwt3](5:29:30 PM –
6/11/2017) (Restriction Releaser)
[Root:Win32k.sys] Design-Terror-Ghost-Win7 (Ghost Window) (terminable) – Win10/8
(Persistence-Winlogout-Bug) Windows Klasse (quadruple kill) gestoppt! Ring-Wächter [Hgwt3]
(5:29:30 PM – 6/11/2017) (Restriction Releaser)
Inhalt in die Zwischenablage kopiert!
/
IT-Security-Archive
24. April 2017 ·
Variable Kill Timer…no other Security Product has this feature…
It destroys all attempts of the CIA to gain superiority on my system…
/
Starte Scan nach Adware, Spyware, Risks, Worms, Keyloggern, Trojanern, Malware und Viren! (V11.11)
__________________________________________________________________________________________
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess entdeckt! (Prozess
Heuristik 5)
__________________________________________________________________________________________
System Information4: NT Version: 6.1 BuildNr.: 7601 Organization: Microsoft
System Information5: Bekannte Sandboxen: COMODO V.8.x(7.x/6.x) /
System Information6: Bekannte virtuelle Machine: NEIN (reales System)
System Information7: Uhrzeit: 21:52:34 und Datum: 20.04.2017
__________________________________________________________________________________________
Peerblock reaktiviert! (21:52:35 – 20.04.2017) (Peerblock-Surveillor)
Free Firewall Tray reaktiviert! (21:52:35 – 20.04.2017) (FreeFirewallTray-Surveillor)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Win7/8 Consent.exe-Freeze/UDP Backdoor/GovWare! Evtl. Unknown.Malware.Exploit!(2014) Prozess gestoppt! (Prozess
Heuristik 5)
Inhalt in die Zwischenablage kopiert!
IT-Security-Archive · 24. April 2017 ·


IT-Security-Archive via Comodo Cybersecurity
1. Januar 2014 ·
„Every day more NSA intrusions are discovered. Many assumed that in the Snowden leaks, the worst of the worst had been brought to our attention. It seems that was just the tip of the iceberg.“
http://www.spiegel.de/international/world/catalog-reveals-nsa-has-back-doors-for-numerous-devices-a-940994.html
IT-Security-Archive
4. November 2013 ·
„04.11.2013, 16:28
BadBIOS: Potentieller Supervirus befällt alle Systeme
BadBIOS: Der mögliche Virus kann sich über Audiosignale weiterverbreiten.
Unter dem Namen „BadBIOS“ kursiert laut einem Sicherheitsforscher derzeit ein bislang unbekannter Super-Schädling im Netz: Die Malware infiziert Rechner unabhängig vom Betriebssystem, löscht beliebige Daten und ändert Einstellungen. Der Schädling verbreitet sich der Beschreibung zufolge ausschließlich über USB-Geräte und befällt anschließend das BIOS des Rechners. Dementsprechend spielt es keine Rolle, welches Betriebssystem auf dem PC läuft: BadBIOS ist in der Lage, sowohl Windows- als auch OS X und OpenBSD-Systeme zu infizieren.
BIOS-Infektion per USB-Stick
Wie genau die Infektion gelingt, ist derzeit noch nicht bekannt. Klar scheint aber, dass die Malware eine bislang unentdeckte Schwachstelle im USB-Standard zur Verbreitung ausnutzt. Dabei könnte der Schädling die Firmware von USB-Geräten gegen eine modifizierte Version austauschen und so zum Beispiel einen Pufferüberlauf erzeugen, um den Schadcode einzuschleusen. Die exakten Verhaltensmuster von BadBIOS seien nur schwer herauszufinden, da sich der Schädling gut vor Analysen verstecken könne: Die Datenübertragung zu seinen Kontrollservern soll BadBIOS über eine verschlüsselte IPv6-Verbindung aufbauen. Liegt keine Netzwerkverbindung vor, kann BadBIOS offenbar andere Rechner in der Nähe über unhörbare Audiosignale erreichen.
Zu gefährlich um wahr zu sein
Entdeckt wurde BadBIOS vom Sicherheitsforscher Dragos Ruiu, der laut eigenen Angaben bereits vor drei Jahren mit dem Schädling infiziert wurde. Neben Informationen zur Malware selbst fehlen jedoch noch stichhaltige Beweise seitens des Entdeckers: Der Beschreibung zufolge würde es sich bei BadBIOS um einen extrem ausgeklügelten Schädling handeln, der herkömmlicher Malware weit voraus wäre. Dragos Ruiu hat der Sicherheitsfirma Sophos jedoch bereits angeboten, ein Sample von BadBIOS zur Verfügung zu stellen. (mag)“
//Source: chip.de/news/BadBIOS-Potentieller-Supervirus-befaellt-alle-Systeme_65235066.html
IT-Security-Archive · 6. November 2012 ·
Blocked… guess why… ;-))

Forensical Backtracking of Rootkit Zombiehost.Deploy.Akaimai.FB.Gov Invaders Next Round..
Forensical Backtracking of Rootkit Zombiehost.Deploy.Akaimai.FB.Gov Invaders – Next Round – points to MIT.
Archontic AI Intrusion and Global Infiltration Alert… Criminal Invasion…
Zombiehost has a Anti-PB-Firewall-Revival Methodism on Microsoft Windows 10 – 64 Bit infiltrated Systems – when Antikeymagic HE Edition/PV wants to revive essential Firewalls – unless Zombiehost is not deactivated – Zombiehost generates a BSOD as a preemptive defense mechanism – in that way it tries to safeguard the trojan spy intrusion mechanism of the Shadow Gov Crooks – The moment Zombiehost is stopped the Firewall can be reactivated and the Crooks can be backtracked.
![]()
GOD BLOCKED THE FEDERAL FASCIS TROJAN OF FACE-CIA-BUG-BOOK.
Zombiehost unmasked Video and Double Firewall Bypass Example
Zombiehost unmasked Video and Double Firewall Bypass Example
____________________________________________________________
Win10Zombiehost_und_DoubleFirewallBypassCFP10FF14Beispiel_SoftwareFailures_2017_08_23
I Found a Comodo Vulnerability by chance… (it is a manual manipulation by accident which probably could disable most firewalls, but there should be a network integrity check in all Firewalls, just in case) I mean the FaceBUG.Fed. Trojan aka Akamai.Deploy.Zombiehost bypasses CFP by default, but this bypass DEMO has nothing to do with Zombiehost.
It is just an integrity check failure of Comodo v.10.x. The other F.Firewall seems to be affected by Zombiehost Firewall Bypass. As always usual Antivirus detects nothing,
except Antikeymagic v.11.x and RKiller 12.x (but incapable of removal)…
Software failed Firewalls: Comodo v.10. / F. Firewall v.1.4x / PBlock 1.2
Failed Antivirus:/Antitrojan/Antispy-Tools: Super Antispy, Stinger McAfee and high likely most other mainstream Secuity Tools will fail…more Tests will follow.
Successful Partial Detection: Antikeymagic v.10.x, RKiller 12.x (Removal Failure).
Download Win10Zombiehost_und_FirewallBypassCFP10FF14Bsp_SoftwareFailures_2017_08_2.mp4
Facebooks Federal Trojan decyphered aka Zombiehost aka PID6.DOD.NSA.Backdoor
Facebooks Federal Trojan decyphered aka Zombiehost aka PID6.DOD.NSA.Backdoor / Unmasked by IVMUP 23.8.2017
_____________________________________________________________________________
Find the fault… / Finde den Fehler…
FaceBUG.Zombiehost.Fed.Trojan.IP…
They sabotage PBlock in Zero.Access.Style…

____________________________________________________
https://infinityexpression.com/2014/12/stealth-system-process-walker-malware-detected-consent-exe-udp-backdoor/
https://infinityexpression.com/2015/10/623/

Antikeymagic successful 3rdParty Security Protection feature – starting at Level 10. (Crystalline Editions)
Stealth System Process Walker Malware Detected: Consent.exe UDP Backdoor
Stealth System Process Walker Malware Detected: Consent.exe – Windows Internal UDP Covert Backdoor.
__________________________________________________________________________
System Process Walker… Bypassing LUA/UAC/Virtualization/Firewalls/AVs/Proxies etc… Windows Fake Security is transforming UAC into a covert communication, control and spy channel. The true reason for preparing the world and all the people to Facebook as a command and control central node of the largest surveillance and remote control base for the agencies and the governments.
TOR or Firewalls aren´t able to prevent governmental spying if „system process walker“ – as I call it, inject itself into consent.exe or any other host or exe process, that may be available. As a rule Firewalls remain quiet and become udp backdoored themselves, no matter which one. Rude multi-layered IP-Filtering may be helfpful, but is no guarantee, because this stealth thing is able to disable virtually all security protection.
The strange thing is, that the Windows Master Key Backdoor (used by governmental agencies or other secret intrusion groups) is able to enter either via Limelight Networks or Akamai Tech Inc.
Consent.exe UDP turns into TCP-Transmission to Facebook Central-Node Akamai Tech Inc. (deploy.xyz Malware). My assumption is – so far – that svchost.exe is backdoored by default, as a master key in all Windows NT 6.x Windows, in that way, that Facebook is able to get remote control via Akamai Tech Inc. (deploy.xyz Malware). Furthermore the Browser is generally UDP-Backdoored (0.0.0.0) (normally invisible) as a primary layer, if the other system backdoors might be closed.
One Example: Microsoft Windows tries several times to connect via Limelight Networks Inc. (This game started already in Windows XP and hasn´t stopped until now…) Some variants use Svchost-Injection (Zombie-Method) to connect via NSA to Facebook (Akamai Inc.) Another Variant from 2008 uses Winlogon-Injection Method to Limelight Inc. Probably all the same Govware
Microsoft, the government or their potential agency contractors use consent.exe as selective Antispy Killer.
Consent.exe as LUA/UAC Backdoor.Exploit with AV-Killer/Antispy-Killer properties…
Comodo is also affected by this stealth UDP leak, which backdoors all cmdagent.exe´s, no matter which version, 8.x, 7.x, 6.x, 5.x, 4.x, 3.x… etc. But this is not directly the Problem of Comodo, either a deliberate system architecture error of Microsoft Windows.
Nobody has written about the system-wide UDP Backdoor in Windows NT 6.x… (especially Windows 7) – then I need to do this… This is an interesting thing, probably the main access method of the NSA and Facebook as a central connection node.
Niemand hat bisher über den systemweiten UDP-Backdoor in Windows NT 6.x geschrieben… (speziell Windows 7) – dann muss ich das tun…. Das ist eine interessante Sache, wahrscheinlich die Hauptzugriffsmethode der NSA und Facebook als Zentralverbindungsknoten.
____________________________________________________________________________________________
Consent.exe is a User Account Control process.
Erscheint manchmal beim windows start im log fenster der firewall events von comodo personal firewall, dannach aber verschwindet der eintrag aus dem log (!!!) und stattdessen taucht scvhost,exe auf.
Wie Ich Bin
It took all 100 percent of my laptop CPU – I couldn’t do anything. Then after about 90 secs it was gone and everything back to normal!
Brad
Similar sightings as above. Noticed browser open in the background (flash upon closing and low level duplicate process concurrently) and checked logs n task monitor continuously. It seems to come and go in 2000sec intevals. The processor spins up on ocassion perhaps lots of udp in the background. Estensive use of placeholders in the URL’s. Specificly I am unsure what it is but t has several charateristics of malware.I am shocked Norton IS didn’t pick it up, That is what baffles me.
Carl